Originating Author: Kaushik Das
Enterprise employees like to conduct important business over mobile phones just as they would have done using their desk phones. In addition, enterprises rely heavily on cellular-based voice communication because it makes them more agile and responsive when facing new challenges such as those deriving from globalization and serving a geographically diverse workforce. In order to achieve this, however, enterprise voice communication demands rock-solid security outside the enterprise premises along with real-time communications in every aspect of their operations. Since over-the-air communications is now prime target for communications eavesdropping and tampering, mobile voice calls (over cellular-based voice networks) are not secure yet to the level desired by enterprises.
The main challenges:
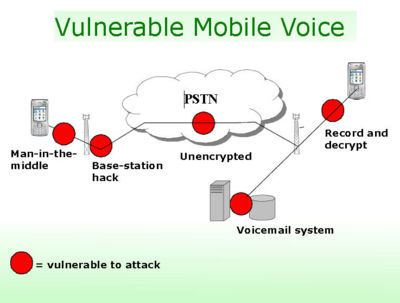
- Mobile voice calls are not secure
- Whereas data traffic is protected, voice is not
- GSM encryption is not always turned on by operator
- Security is cracked in seconds and cheaply
- Abusing voicemail is easy
- First target for corporate espionage attacks - remote access, simple PIN
- During retrieval, information is tapped as voice calls
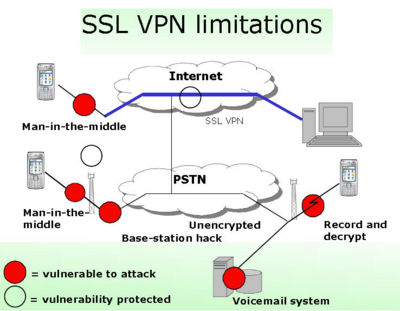
- Standard VPNs are inadequate for voice
- Security doesn't reach the end-point voice device
- Bandwidth requirements limit scalability
The mobile voice security is an extremely important component of IT infrastructure for the following:
- Government officials
- Police
- Military
- Corporate decision makers
- Healthcare professionals
- Pharmaceuticals
- Financial services
- Insurance providers
 Source: Cellcrypt - with permission
Source: Cellcrypt - with permission
 Source: Cellcrypt - with permission
Source: Cellcrypt - with permission
Current market scenario (from Gartner, In-stat):
- Blackberry is defacto standard in government and finance sectors
- 8 million installed base, 3.5m shipped ‘06
- Multimedia VPN to close VOIP end-point security gap
- 81m SmartPhones shipped in 2006, 66% ’05/’06, Symbian dominates
- SSL VPN market will reach $881 million by 2008
Capability of secured (mobile) voice communication
Enterprises like to secure voice communication, i.e secure both voice calls and voice mails. Mobile voice security has the following capabilities when implemented.
- Protect vulnerable communication
Voice passes through a safe enclosure (of encryption), making eavesdropping as well as tampering extremely difficult.
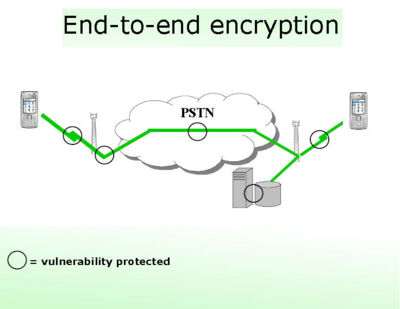
- End-to-end encryption
End-to-end encryption ensures maximum security for an enterprise. The end result is a reliable and secured voice communication that you can only get from your desk phones.
- Protect privacy
Sophisticated technology deters any interception of your conversation with rock-hard reliability.
- Peace of mind with secure communication and enhance productivity
When you realize that every word you utter will pass through a high security zone, you'll enjoy speaking in a relaxed atmosphere and with peace of mind. You'll do more with your mobile phones resulting in enhanced productivity.
Specific operational goals of secured (mobile) voice communication
As wireless voice networks are more susceptible to invasion, it's difficult to calculate the cost of security breached in real currency value. Security costs arising out of unsecured and compromised wireless voice networks are generally difficult to quantify but one can estimate it by measuring the repercussions arising in the form of lost productivity, direct and indirect business losses, crucial information leakage etc.
The goal is now to secure voice communication, i.e secure both voice calls and voice mails. When implementing security solutions, enterprises consider mainly the following:
- End-to-end encryption
- Software-only solution that removes compromises of specialist hardware encryption solutions
 Source: Cellcrypt - with permission
Source: Cellcrypt - with permission
Enterprises look for:
- Highly secure mobile-to-mobile voice
- Secure client software scaled for smart phones
- Bandwidth optimised Multimedia VPN
- Secure push voice mail
- Encrypted messages delivered to phone
- Access in any order through visual display
- No compromise on phone features
- Software-only, on standard phones
- All standard SmartPhone features work
- Standard SmartPhone battery life