Portal:Mobile Enterprise
From Wikibon
| Line 1: | Line 1: | ||
| + | <meta name="description" content="The Wikibon Mobile Enterprise Technology Portal contains mobile enterprise industry research, articles, expert opinion, case studies, and mobile enterprise related company profiles." /> | ||
| + | <meta name="title" content="Mobile Enterprise Technology Portal" /> | ||
| + | |||
| + | The Wikibon Mobile Enterprise Technology Portal contains mobile enterprise industry research, articles, expert opinion, case studies, and mobile enterprise related company profiles. | ||
| + | |||
__NOTOC__ | __NOTOC__ | ||
{| | {| | ||
| Line 23: | Line 28: | ||
</p> | </p> | ||
[[Architecting wireless email | read more...]] | [[Architecting wireless email | read more...]] | ||
| - | |} | + | |}[[Category:Mobile Enterprise Wikitips]][[Category: Wikitips]] |
Revision as of 18:55, 17 September 2009
The Wikibon Mobile Enterprise Technology Portal contains mobile enterprise industry research, articles, expert opinion, case studies, and mobile enterprise related company profiles.
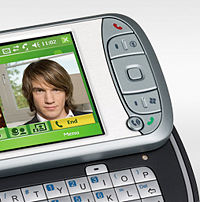
WikitipBuild expertise in New Handheld PlatformsIT organizations and consultants who get ahead of the game and build development expertise on the iPhone/iPod Touch and Android now will have a leg up as this market grows. If you have not already, you should invest in at least one or two iPhones and two Android phones just to become familiar with these next generation platforms, and you should either build development capabilities on this platform internally or identify a good consulting firm that can provide that capability when you need it. |
Featured Case StudySafeguarding Enterprise Voice Communication over WiFiEnterprises are showing a strong interest on wireless voice technology over the standard WiFi networks for its attractive features such as lower phone bills, centralized management, or fast deployments. However these wireless voice networks are susceptible to usual attacks like viruses, spam, phishing, hacking, stolen data, denial of service (DoS), voice injections, man in the middle attacks, call hijacking, eavesdropping etc. The security of these networks become a major concern for enterprises because IT managers have no or very little knowledge how to protect voice networks. |
|
Featured How-To Note |
Architecting Wireless EmailWireless email is an important business tool for today's enterprises and an entrepreneurial solution to maximize the employees’ business potential and gain a competitive edge. Since businesses now send as much as 60% of their business-critical data via email, accessing emails wirelessly means business success for many organizations by providing rapid customer communication, faster decision-making and collaboration from distant places. | |||