Portal:Mobile Enterprise
From Wikibon
| (13 intermediate revisions not shown) | |||
| Line 1: | Line 1: | ||
| + | <!--|body|--><meta name="description" content="The Wikibon Mobile Enterprise Technology Portal contains mobile enterprise industry research, articles, expert opinion, case studies, and mobile enterprise related company profiles." /> | ||
| + | <meta name="title" content="Mobile Enterprise Technology Portal" /> | ||
| + | |||
| + | The Wikibon Mobile Enterprise Technology Portal contains mobile enterprise industry research, articles, expert opinion, case studies, and mobile enterprise related company profiles. | ||
| + | [http://www.rushtonfinancial.com.au Best Investment] | [http://www.rushtonfinancial.com.au/why-invest Managed Funds] | [http://www.rushtonfinancial.com.au/about-us Mutual Funds Australia] | ||
| + | |||
| + | {| class="wikitable" style="font-size: 80%; text-align: center; width: 95%;" | ||
| + | ![[Image:LinkedIn.gif|100px|link=http://www.linkedin.com/groups?gid=835317&trk=hb_side_g]] | ||
| + | |[[Image:facebook.jpeg|100px|link=http://www.facebook.com/pages/Wikibon/6191646228]] | ||
| + | |[[Image:twitter.jpg|100px|link=http://twitter.com/wikibon]] | ||
| + | |[[Image:blog-2.jpg|100px|link=http://wikibon.org/blog]] | ||
| + | |- | ||
| + | |[http://www.linkedin.com/groups?gid=835317&trk=hb_side_g >>Join our Group] | ||
| + | |[http://www.facebook.com/pages/Wikibon/6191646228 >>Become a Fan] | ||
| + | |[http://twitter.com/wikibon >>Follow @Wikibon] | ||
| + | |[http://wikibon.org/blog >>Read the Blog] | ||
| + | |-} | ||
| + | |||
| + | |||
__NOTOC__ | __NOTOC__ | ||
{| | {| | ||
|+ | |+ | ||
| - | | colspan="2" | <tipoftheday category=" | + | | colspan="2" | <tipoftheday category="Mobile_Enterprise_Wikitips" /> |
| + | |||
| + | [[:Category:Mobile Enterprise Wikitips|Browse all Mobile Enterprise Wikitips]] | ||
|+ | |+ | ||
| width="50%" valign="top" | | | width="50%" valign="top" | | ||
| Line 11: | Line 32: | ||
[[Safeguarding enterprise voice communication over WiFi networks | read more...]] | [[Safeguarding enterprise voice communication over WiFi networks | read more...]] | ||
| valign="top" | | | valign="top" | | ||
| - | {{Mobile | + | {{Mobile Enterprise professional alerts 2}} |
|+ | |+ | ||
| valign="top" | | | valign="top" | | ||
===Featured How-To Note=== | ===Featured How-To Note=== | ||
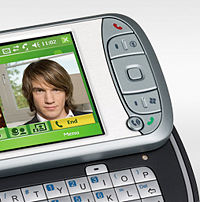
[[Image:Mobile How-to Note Image.jpg|left|200px]] | [[Image:Mobile How-to Note Image.jpg|left|200px]] | ||
| - | + | ||
| + | |||
==[[Architecting wireless email|Architecting Wireless Email]]== | ==[[Architecting wireless email|Architecting Wireless Email]]== | ||
<p style="color: #666;">Wireless email is an important business tool for today's enterprises and an entrepreneurial solution to maximize the employees’ business potential and gain a competitive edge. Since businesses now send as much as 60% of their business-critical data via email, accessing emails wirelessly means business success for many organizations by providing rapid customer communication, faster decision-making and collaboration from distant places. | <p style="color: #666;">Wireless email is an important business tool for today's enterprises and an entrepreneurial solution to maximize the employees’ business potential and gain a competitive edge. Since businesses now send as much as 60% of their business-critical data via email, accessing emails wirelessly means business success for many organizations by providing rapid customer communication, faster decision-making and collaboration from distant places. | ||
</p> | </p> | ||
[[Architecting wireless email | read more...]] | [[Architecting wireless email | read more...]] | ||
| - | |} | + | |}<!--|body|--> |
| - | + | ||
| - | + | ||
| - | + | ||
| + | '''Action Item: <!--|actionitem|-->[http://www.detikauto.com Aksesoris Mobil] | [http://www.tokobungasabana.com Florist Jakarta] | [http://trimasjaya.com/products/railing_tangga/index.html Railing Tangga] | [http://www.forklift.co.id Rental Forklift]<!--|actionitem|--> | ||
| + | ''Footnotes: <!--|footnotes|--><!--|footnotes|--> | ||
| - | [[Category: | + | [[Category:Information Security Wikitips]][[Category: Mobile Enterprise Wikitips]][[Category: Professional alerts]][[Category: Security]][[Category: Storage]][[Category: Storage asset management]][[Category: Storage professional alerts]][[Category: Storage security]][[Category: Wikitips]] |
Current revision as of 03:38, 20 January 2016
The Wikibon Mobile Enterprise Technology Portal contains mobile enterprise industry research, articles, expert opinion, case studies, and mobile enterprise related company profiles. Best Investment | Managed Funds | Mutual Funds Australia
| >>Join our Group | >>Become a Fan | >>Follow @Wikibon | >>Read the Blog | |||||||||||||||||||
WikitipPortal:Storage
The Wikibon Data Storage Portal contains data storage industry research, articles, expert opinion, case studies, and data storage company profiles.
|
Featured Case StudySafeguarding Enterprise Voice Communication over WiFiEnterprises are showing a strong interest on wireless voice technology over the standard WiFi networks for its attractive features such as lower phone bills, centralized management, or fast deployments. However these wireless voice networks are susceptible to usual attacks like viruses, spam, phishing, hacking, stolen data, denial of service (DoS), voice injections, man in the middle attacks, call hijacking, eavesdropping etc. The security of these networks become a major concern for enterprises because IT managers have no or very little knowledge how to protect voice networks. |
|
Featured How-To Note
Architecting Wireless EmailWireless email is an important business tool for today's enterprises and an entrepreneurial solution to maximize the employees’ business potential and gain a competitive edge. Since businesses now send as much as 60% of their business-critical data via email, accessing emails wirelessly means business success for many organizations by providing rapid customer communication, faster decision-making and collaboration from distant places. | |||||||||||||||||||
Action Item: Aksesoris Mobil | Florist Jakarta | Railing Tangga | Rental Forklift
Footnotes: