Portal:Information Security
From Wikibon
| Line 15: | Line 15: | ||
====[[Data encryption strategies]]==== | ====[[Data encryption strategies]]==== | ||
| - | <p style="color: #666;">.. | + | <p style="color: #666;">As the amount of digital data grows, so does the exposure to data loss. It is difficult to find a day when there hasn’t been a high-profile data security incident. The risk has reached such a level that data encryption is being implemented for stored data and mobile data, in addition to the traditional use of encrypting data in transit via the network. </p> |
| - | [[ | + | [[Data encryption strategies|read more...]] |
| valign="top" | | | valign="top" | | ||
{{Information Security Professional Alerts}} | {{Information Security Professional Alerts}} | ||
| Line 26: | Line 26: | ||
|} | |} | ||
| - | [[Category:Careers]][[Category: Careers wikitips]][[Category: Information Management wikitips]][[Category: Information Security Wikitips]][[Category: Mobile Enterprise Wikitips]][[Category: Storage security]][[Category: TreeTop Technologies]][[Category: Wikitips]] | + | [[Category:Careers]][[Category: Careers wikitips]][[Category: Enterprise mobile wikitips]][[Category: Information Management wikitips]][[Category: Information Security Wikitips]][[Category: Mobile Enterprise Wikitips]][[Category: Storage security]][[Category: TreeTop Technologies]][[Category: Wikitips]] |
Revision as of 03:38, 30 September 2009
Welcome to the Wikibon Information Security Portal. The Information Security Portal is a resource for IT professionals interested in learning from peers and sharing knowledge with other practitioners.
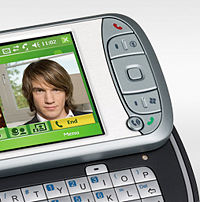
WikitipPortal:Mobile Enterprise
The Wikibon Mobile Enterprise Technology Portal contains mobile enterprise industry research, articles, expert opinion, case studies, and mobile enterprise related company profiles. Best Investment | Managed Funds | Mutual Funds Australia
Action Item: Aksesoris Mobil | Florist Jakarta | Railing Tangga | Rental Forklift Footnotes: |
Featured ResearchData encryption strategiesAs the amount of digital data grows, so does the exposure to data loss. It is difficult to find a day when there hasn’t been a high-profile data security incident. The risk has reached such a level that data encryption is being implemented for stored data and mobile data, in addition to the traditional use of encrypting data in transit via the network. |
|
Featured Success Story | ||||||||||||||||||||||||||||||||||